Appendix B Wireless LANs
VMG5313-B10A/-B30A Series User’s Guide
371
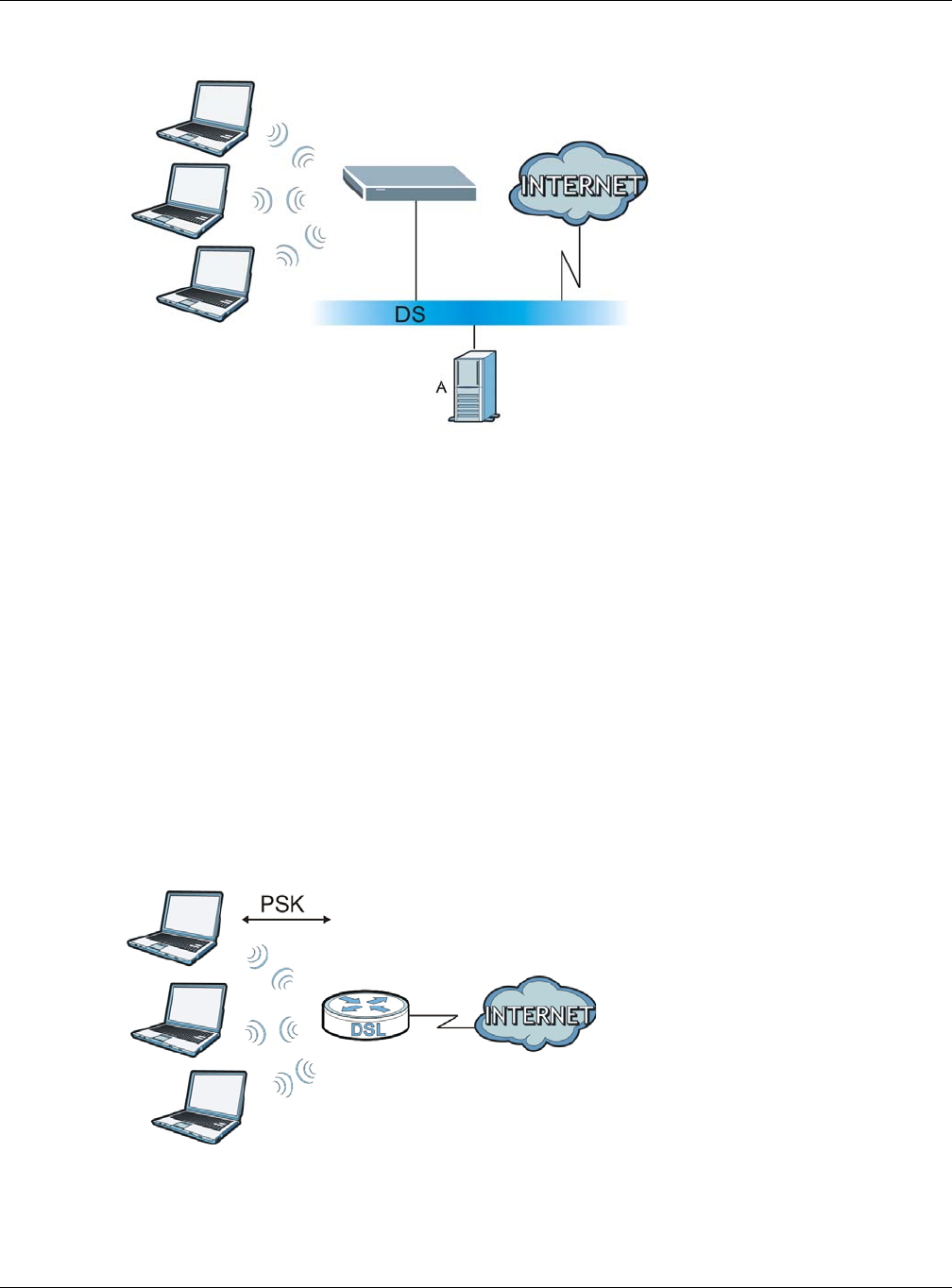
Figure 191 WPA(2) with RADIUS Application Example
WPA(2)-PSK Application Example
A WPA(2)-PSK application looks as follows.
1 First enter identical passwords into the AP and all wireless clients. The Pre-Shared Key (PSK) must
consist of between 8 and 63 ASCII characters or 64 hexadecimal characters (including spaces and
symbols).
2 The AP checks each wireless client's password and allows it to join the network only if the password
matches.
3 The AP and wireless clients generate a common PMK (Pairwise Master Key). The key itself is not
sent over the network, but is derived from the PSK and the SSID.
4 The AP and wireless clients use the TKIP or AES encryption process, the PMK and information
exchanged in a handshake to create temporal encryption keys. They use these keys to encrypt data
exchanged between them.
Figure 192 WPA(2)-PSK Authentication


















