Chapter 17 VPN
FMG3024-D10A / FMG3025-D10A Series User’s Guide
172
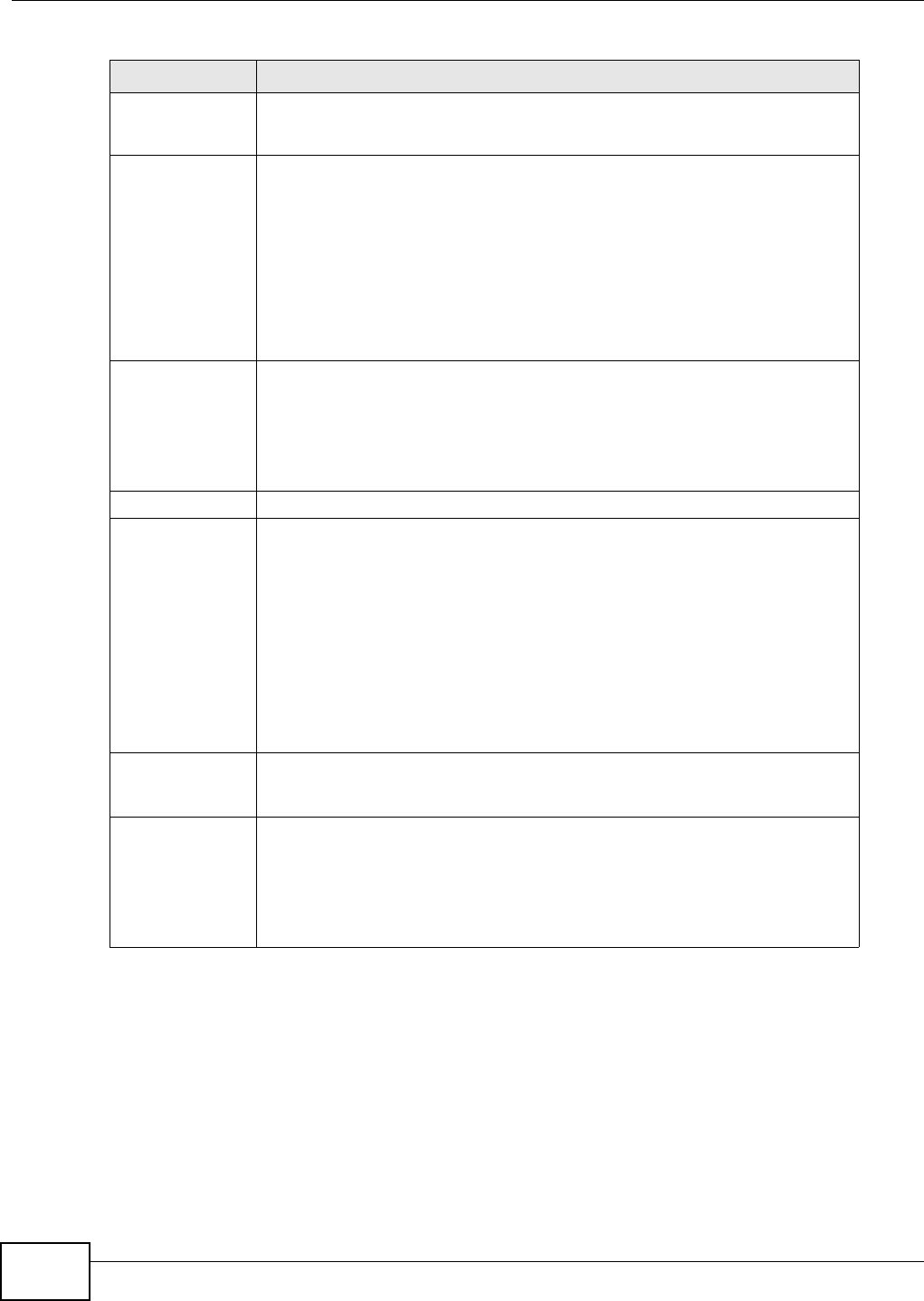
Authentication
Algorithm
Select which hash algorithm to use to authenticate packet data. Choices are
MD5, SHA1, SHA2-256 and SHA2-512. SHA is generally considered stronger
than MD5, but it is also slower.
DH Select which Diffie-Hellman key group you want to use for encryption keys.
Choices are:
Diffie-Hellman Group2 - use a 1024-bit random number
Diffie-Hellman Group5 - use a 1536-bit random number
Diffie-Hellman Group14 - use a 2048-bit random number
The longer the key, the more secure the encryption, but also the longer it takes
to encrypt and decrypt information. Both routers must use the same DH key
group.
SA Life Time Define the length of time before an IPSec SA automatically renegotiates in this
field.
A short SA Life Time increases security by forcing the two VPN gateways to
update the encryption and authentication keys. However, every time the VPN
tunnel renegotiates, all users accessing remote resources are temporarily
disconnected.
Phase 2
Encryption
Algorithm
Select which key size and encryption algorithm to use in the IKE SA. Choices
are:
DES - a 56-bit key with the DES encryption algorithm
3DES - a 168-bit key with the DES encryption algorithm
AES128 - a 128-bit key with the AES encryption algorithm
AES256 - a 256-bit key with the AES encryption algorithm
The Device and the remote IPSec router must use the same key size and
encryption algorithm. Longer keys require more processing power, resulting in
increased latency and decreased throughput.
Authentication
Algorithm
Select which hash algorithm to use to authenticate packet data. Choices are
MD5, SHA1. SHA is generally considered stronger than MD5, but it is also
slower.
SA Life Time Define the length of time before an IPSec SA automatically renegotiates in this
field.
A short SA Life Time increases security by forcing the two VPN gateways to
update the encryption and authentication keys. However, every time the VPN
tunnel renegotiates, all users accessing remote resources are temporarily
disconnected.
Table 51 IPSec VPN: Add
LABEL DESCRIPTION


















