Configuring IP Addressing
Configuring Network Address Translation
IPC-41
Cisco IOS IP Configuration Guide
Note The access list must permit only those addresses that are to be translated. (Remember that there is an
implicit “deny all” at the end of each access list.) An access list that is too permissive can lead to
unpredictable results.
Packets that enter the router through the inside interface and packets sourced from the router are
checked against the access list for possible NAT candidates. The access list is used to specify which
traffic is to be translated.
See the “Overloading Inside Global Addresses Example” section at the end of this chapter for an
example of overloading inside global addresses.
Translating Overlapping Addresses
The NAT overview discusses translating IP addresses, which could occur because your IP addresses are
not legal, officially assigned IP addresses. Perhaps you chose IP addresses that officially belong to
another network. The case of an address used both illegally and legally is called overlapping. You can
use NAT to translate inside addresses that overlap with outside addresses. Use this feature if your IP
addresses in the stub network are legitimate IP addresses belonging to another network, and you want to
communicate with those hosts or routers.
Figure 6 shows how NAT translates overlapping networks.
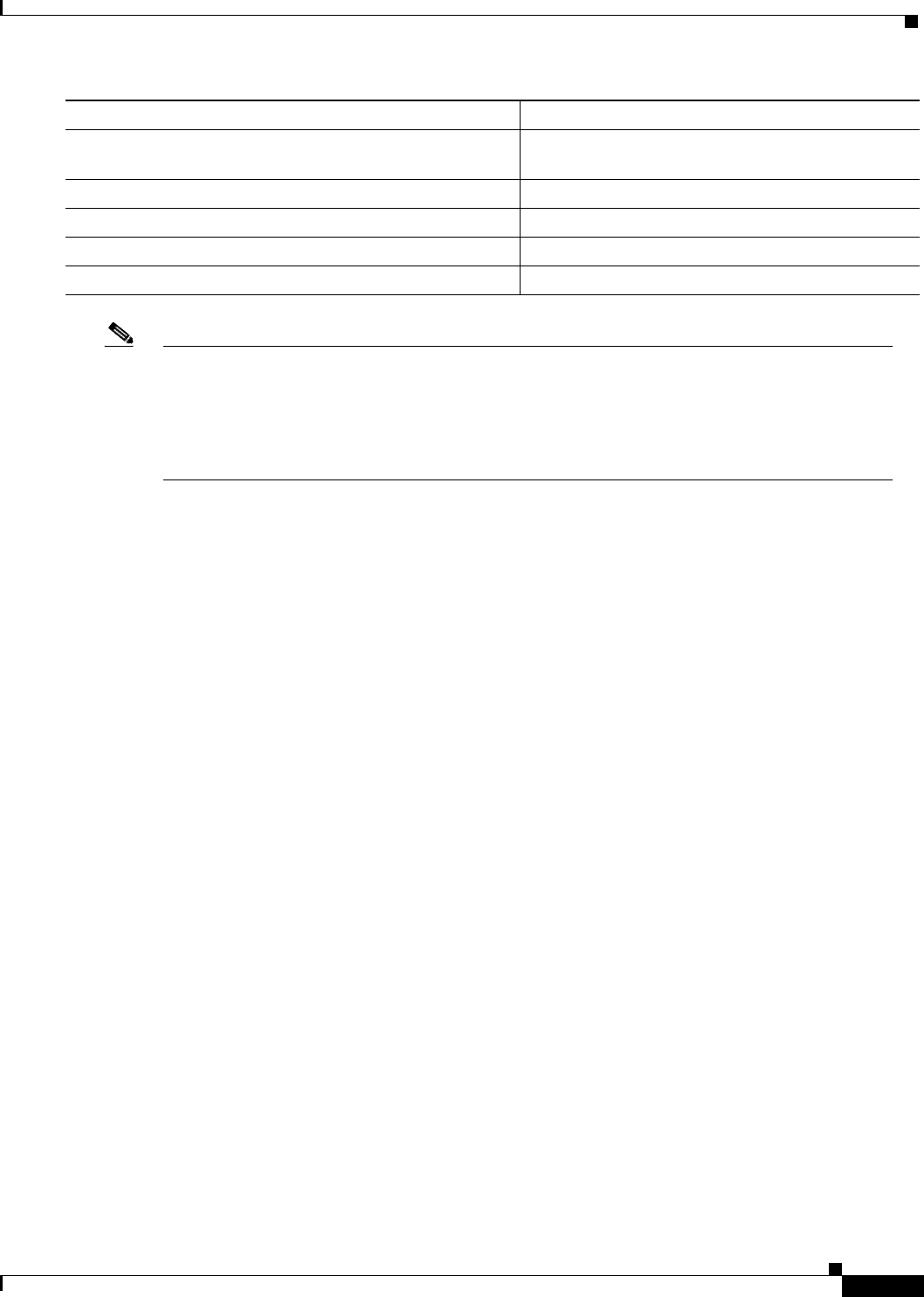
Step 3
Router(config)# ip nat inside source list
access-list-number pool name overload
Establishes dynamic source translation, specifying
the access list defined in the prior step.
Step 4
Router(config)# interface type number
Specifies the inside interface.
Step 5
Router(config-if)# ip nat inside
Marks the interface as connected to the inside.
Step 6
Router(config)# interface type number
Specifies the outside interface.
Step 7
Router(config-if)# ip nat outside
Marks the interface as connected to the outside.
Command Purpose


















